Responding to Declared Incidents
On this page
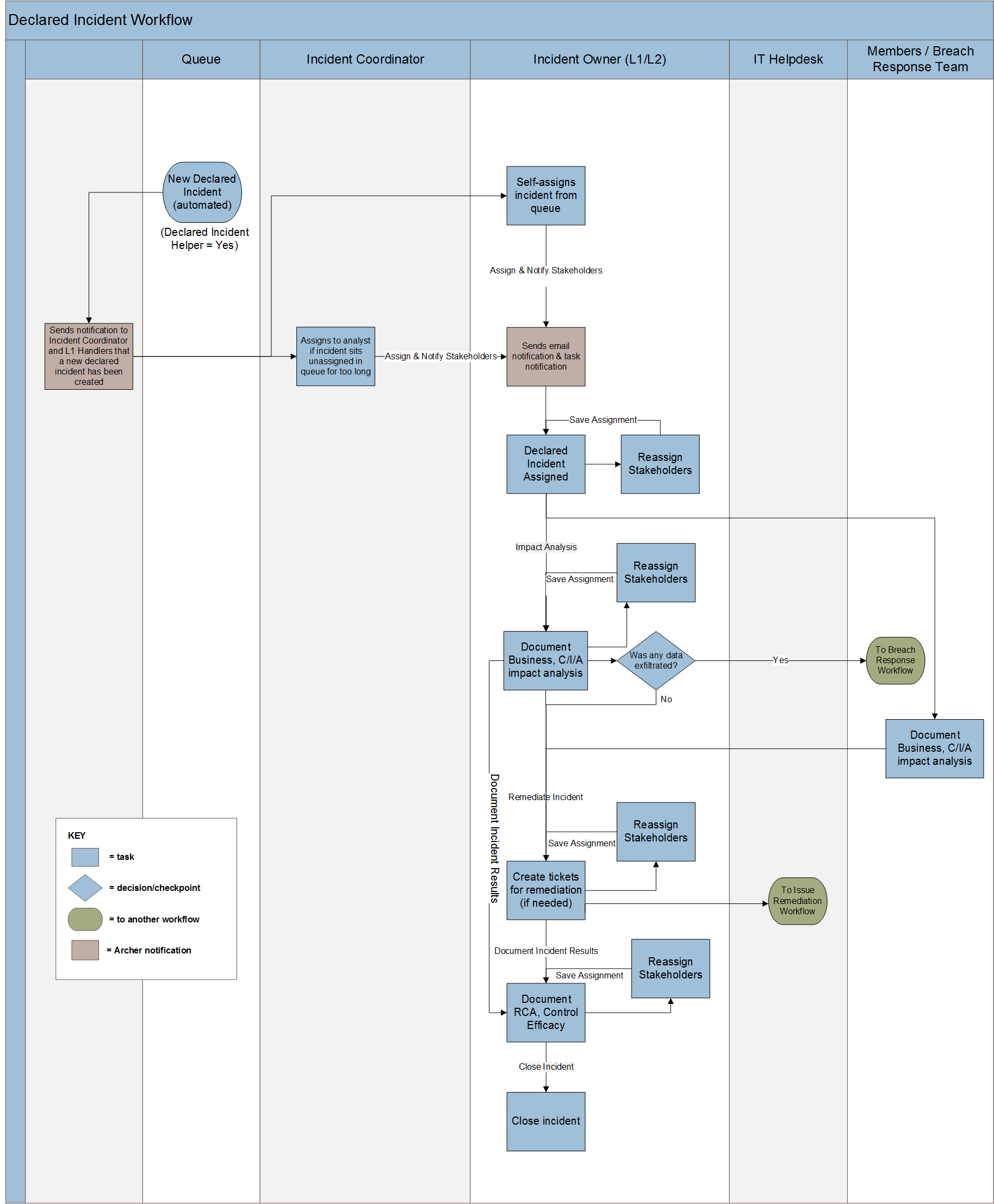
Declared Incident Workflow
The Declared Incident advanced workflow provides you with a simplified process for resolving declared incidents. Using the Declared Incident workflow, you can directly engage business stakeholders as part of the impact analysis and breach response process, and reduce the time required to resolve critical declared incidents.
The Cyber Incident & Breach Response use case is built to support the following Declared Incident workflow:
Download the source file of the diagram here: Cyber Incident & Breach Response Declared Incident Workflow Diagram
To make use of the Declared Incident advanced workflow process, you must send data to Archer using APIs. For information on the required fields, see Enabling the Declared Incident Advanced Workflow.
Tasks to Respond to Declared Incidents
Here are the tasks to respond to declared incidents:
-
Assign the relevant stakeholders, such as the Incident Owner, Incident Coordinator, and additional team members, and link to the relevant device information.
-
Start the incident review. Review declared incident details, such as Name, Priority, Threat Category, No. Of Alerts, and Device Details. The Incident Owner can optionally override the priority of the declared incident and automatically generate Incident Response Procedures and Incident Response Tasks based on the declared incident Threat Category.
-
Document impact analysis. Engage the business to perform an Impact Assessment, and a Confidentiality, Integrity, and Availability impact analysis on the reported declared incident. Additionally, report any findings to IT System Administrator for remediation and report a data breach when data loss is identified.
-
For each issue that needs remediation, create a new Findings record within the Remediation tab of the Security Incident record. Describe the action to complete, the criticality for the finding, a target queue, and a remediation task type.
-
Document the incident analysis. Provide the incident results, the actors, and techniques that contributed to the incident, the incident target details, and add the security controls associated with discovering the incident.


