NIST National Vulnerability Database (NVD) Integration
The NIST National Vulnerability Database (NVD) is the U.S. government repository of standards-based vulnerability management data. This data enables automation of vulnerability management, security measurement, and compliance. NVD includes databases of security checklists, security related software flaws, misconfigurations, product names, and impact metrics.
Archer Exchange: With the Archer Exchange, the Archer team has created a broad selection of supplemental, value-added offerings to help you get your unique risk management program on the right path, right from the start. You can leverage the Archer Exchange offerings to expand the use of Archer solutions into new business processes and address specific industry, geographic, regulatory, or technical requirements.
To learn more, see NIST National Vulnerability Database (NVD) Integration on the Archer Exchange.
On this page
Release notes
|
Release date |
Release |
Notes |
|---|---|---|
|
6.14 Note: As of 2/11/2026, this version has reached end of product support. Version 2025.04 supports on-premise and SaaS environments. |
September 2025 |
The JavaScript Transporter in Data Feed Manager has been updated to use Fetch instead of Request. Fetch is a modern JavaScript API for making HTTP requests, offering a simpler and more powerful alternative to the older Request library. For more information, see the following blog post: Data Feed Manager JavaScript Transporter Scripts Require Update. |
|
Document Version |
Published Date |
Notes |
|
2025.04 |
July 2025 |
|
|
6.14 |
June 2024 |
Re-Signed JavaScript file. |
|
6.14 |
December 2023 |
NIST has elected to retire its legacy data feeds and the 1.0 APIs and guided existing users to transition to the 2.0 APIs to continue to get NVD data without interruption. The data feed configuration has been changed to JavaScript Transporter Data Feed that fetches the NVD vulnerabilities data through NVD API 2.0. |
|
1.3 |
December 2023 |
Replacement of HTTP Transporter Data feed due to deprecation of legacy NVD API, with NVD JST Data feed |
|
1.2 |
August 2023 |
Update of the NVD Data Request URI |
|
1.1 |
July 2019 |
Conversion from XML to JSON source due to XML source deprecation |
|
1.0 |
December 2023 |
Initial Version |
Overview
The integration of NVD with the Archer IT & Security Vulnerabilities Program use case enables customers to connect the NVD catalog of vulnerabilities using the CVE standard to the asset information within Archer.
Key features & benefits
The NIST NVD integration with Archer enables organizations to:
-
Catalog vulnerabilities using the Common Vulnerability Enumeration (CVE) standard defined by the US Government.
-
Build a base Vulnerability Library recognized as security industry standard.
Prerequisites (ODA and system requirements)
|
Components |
Prerequisites |
|---|---|
|
Archer Solution Area |
IT Security & Risk Management |
|
Archer Use Case |
Archer IT Security Vulnerabilities Program |
|
Archer Applications |
Vulnerability Library, Vulnerability Reference Lists |
|
Uses Custom Objects |
No |
|
Requires Archer On-Demand Application License |
This offering does not require any Archer On-Demand Application licenses. |
|
Supported Archer Environments |
|
|
Partner/Vendor Requirements |
Valid NIST license is required |
Compatible use cases and applications - related applications
|
Application |
Use Case |
Primary Purposes of the Relationship |
|
Vulnerability Library |
IT Securities Vulnerabilities Program (IT Security & Risk Management)
|
|
|
Vulnerability Reference Lists |
IT Securities Vulnerabilities Program (IT Security & Risk Management)
|
|
Additional resources
The following additional resources are available for this offering:
-
Third-party website: https://nvd.nist.gov/
Components
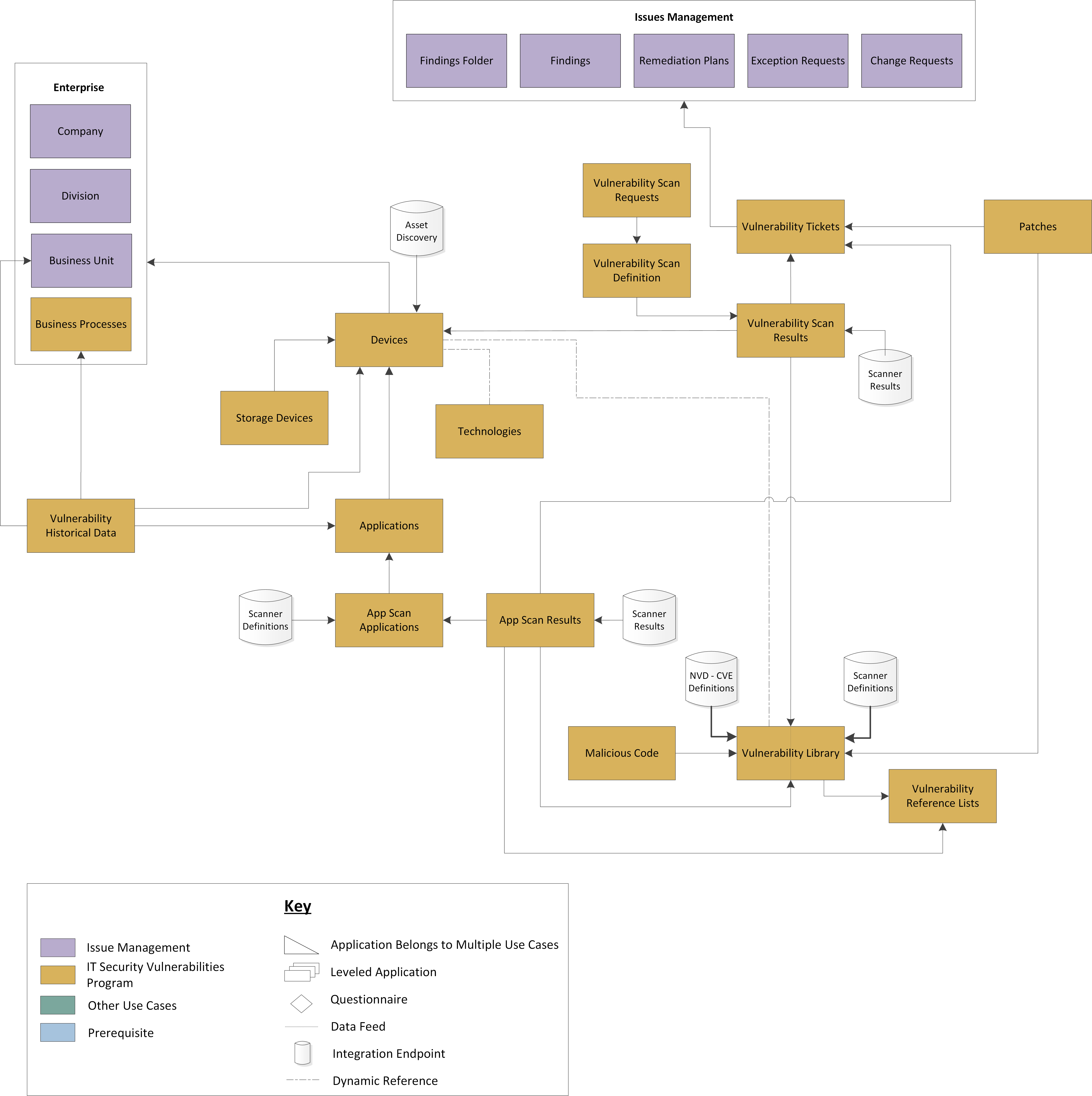
Architecture diagram
The following diagram provides an overview of the integration between NVD and Archer.
Applications
|
Application |
Description |
|
Vulnerability Library |
The Vulnerability Library application represents a catalog of vulnerability data collected from the National Vulnerabilities Database (NVD)/National Institute of Standards and Technology (NIST), Qualys Guard, and Tenable Security Center. The Vulnerability Library is updated each week or month by data feeds depending on the source. The library includes data points such as:
Records can be linked to affected devices, vulnerability scan results, and malicious code found to exploit the vulnerability. The Vulnerability Library also provides a method for generating exception requests, identifying mitigating strategies, and denoting affected ports. By tying vulnerabilities to assets, you can properly analyze, prioritize, and respond proactively to address the threat for vulnerable assets. The Vulnerability Library provides the ability to:
|
|
Vulnerability Reference Lists |
The Vulnerability Reference Lists application provides a repository of public vulnerability references collected from the National Vulnerabilities Database (NVD)/National Institute of Standards and Technology (NIST), Qualys Guard, and Tenable Security Center, based on what vendor you are using to scan. The Vulnerability Reference List is updated based on a user-defined schedule to account for emerging threats. The application provides a list of entries, each containing a vulnerability identification number, a type, and a public reference for known Cyber Security vulnerabilities. The URL found in the application contains a list of public references detailing information about the vulnerability, such as a description, consequences of the vulnerability, and potential mitigation strategies. |
Personas and access roles
The following table describes the functions that make up the application’s organization roles. Depending on the organization of your company, these functions and responsibilities may vary.
|
Function |
Description |
|
ITSVP: Analysts |
This role provides the appropriate access levels to Analysts within the ITSVP use case to perform analysis and classify vulnerabilities accordingly. |
|
ITSVP: Operations |
This role provides the appropriate access levels to Operators within the ITSVP use case. |
|
ITSVP: Executive Management |
This role establishes the rights for Executive Management within the ITSVP use case. Users with this role are provided with read access to ITSVP applications. |
|
ITSVP: Business Management |
This role provides access levels to the appropriate line of business within the ITSVP use case. |
|
ITSVP: Admin |
This role serves as the administrator for the ITSVP use case, providing create, read, update, and delete access rights. |
Setting up the NIST National Vulnerability Database (NVD) data feed
This section provides instructions for configuring the NIST CVE data feed. This document is not intended to suggest optimum installations or configurations.
It is assumed that the reader has both working knowledge of all products involved, and the ability to perform the tasks outlined in this section. Administrators should have access to the product documentation for all products to install the required components.
Important: The integration described in this guide is being provided as a reference implementation for evaluation and testing purposes. It may or may not meet the needs and use cases for your organization. If additional customizations or enhancements are needed, it is recommended that customers contact Archer Professional Services for assistance.
Prerequisites (System Requirements)
The Archer IT Security Vulnerability Program use case must be installed and working prior to the integration. The Vulnerability Library application serves as the target application for the NVD data feed. Perform the necessary tests to confirm that this is true prior to proceeding.
Note: Obtain the installation package from Archer Exchange, ensuring it aligns with your Archer platform release and deployment environment.
Configure JavaScript Transporter Settings
Before you upload a JavaScript file, you must configure JavaScript Transporter settings in the Archer Control Panel.
-
Open the Archer Control Panel.
-
Go to Instance Management > All Instances.
-
Select an instance.
-
On the General tab, go to the JavaScript Transporter section.
-
In the Max Memory Limit field, set the value to 2048 MB (2 GB).
-
In the Script Timeout field, set the value to 120 minutes (2 hours).
-
Require Signature is active by default on install. Signed Certificate Thumbprints are required for all Hosted clients.
-
In the Signing Certificate Thumbprints section, add a thumbprint for each digitally signed JavaScript file.
-
In the Signing Certificate Thumbprints section, double-click an empty cell.
-
Enter the digital thumbprint of the trusted certificate used to sign the JavaScript file.
Note: For more information on how to obtain digital thumbprints, see "Digital Thumbprints" below.
Important: If you enable Require Signature and do not specify thumbprints, JavaScript files will not be accepted by the system.
-
-
-
On the toolbar, click Save.
When running JavaScript data feeds, you can set the system to only allow digitally signed JavaScript files from trusted sources for security considerations.
For a certificate to be trusted, all certificates in the chain, including the Root CA Certificate and Intermediate CA certificates, must be trusted on both the Web Server and Services Server machines.
By default, the Archer Technology LLC certificate is not present on every machine’s root.
-
On the JavaScript file, right-click and select Properties.
-
Click the Digital Signatures tab.
-
From the Signature List window, select Archer Technologies LLC.
-
Click the Details button.
-
Click View Certificate.
-
Click Install Certificate.
-
Select Local Machine.
-
Click Next.
-
Select Place all certificates in the following store, and click Browse.
-
Select Trusted Root Certification Authorities, and click OK.
-
Click Next.
-
Click Finish.
-
-
-
Click OK.
-
On the Web Server and Services Server machines, open the Manage User Certificates program.
-
From the Windows Start menu, launch certmgr. (Manage User Certificates).
-
Navigate to Certificates – Local Computer > Trusted Root Certification Authorities > Certificates.
-
Ensure the following certificates are in the Certificates sub-folder of the Trust Root Certification Authorities folder:
-
Archer Technologies LLC.
-
Archer Security 2048 V3 (Standard certificate).
-
-
-
Verify that the certificate is trusted.
-
Double-click the Archer Technologies LLC certificate.
-
In the Certificate window, click the Certification Path tab.
-
Ensure that the Certificate Status window displays the following message: “This certificate is OK.”
Note: If the Certificate Status window displays a different message, follow the onscreen instructions.
-
-
Obtain the trusted certificate thumbprint.
-
In the Certificate window, click the Details tab.
-
Scroll to and select the Thumbprint field.
The certificate's digital thumbprint appears in the window.
-
Copy the thumbprint.
Note: For information on adding digital thumbprints, see Step 7a of "Configuring the JavaScript Transporter Settings".
-
Set up the NVD data feed
-
Go to the Manage Data Feeds page.
-
From the menu bar, click
 .
. -
Under Integration, click Data Feeds.
-
-
In the Manage Data Feeds section, click Import.
-
Locate and select the .dfx5 file.
-
Click Open.
-
In the General Information section, in the Status field, select Active.
-
In the Additional Properties section, enable Optimize Calculations.
-
Click the Transport tab.
-
In the Transport Configuration section, complete the following:
-
Click Upload.
-
From the Upload JavaScript File dialog, click Add New.
-
Locate and select the .js file and click Open.
-
From the Upload JavaScript File dialog, click OK.
-
-
The JavaScript code allows clients to pass in different variables through the Custom Parameters section. The following table describes the supported values for specific Custom Parameters.
-
For a valid API Key, the limit is 100 requests per minute. The API key can be requested from the following NVD link:
-
Data is retrieved by utilizing the following filter parameters:
-
lastModifiedStartDate
-
lastModifiedEndDate
-
resultsPerPage
-
-
These parameters return only the CVEs that were last modified during the specified period.
-
Both lastModifiedStartDate and lastModifiedEndDate are required.
-
If lastModifiedStartDate is not defined, then the LastRunTime value is used (either as a parameter override, a data feed token, or the default value in the JS code).
-
LastRunTime always incorporates the lastRunTimeOffset parameter when determining a date. (Required)
-
-
If lastModifiedEndDate is not defined, then default to Current Date.
-
If lastModifiedEndDate is set in future to current date, then default to Current Date
-
Utilized only for Base Loads.
-
The code leverages a startIndex parameter that specifies the index of the first CVE to be returned in the response data. Index is zero-based, meaning the first CVE is at index zero. With the combination of resultsPerPage and startIndex, we extract remaining content until totalResults is reached.
-
Defaults = DATE
-
Value range of 100 - 2000. If set outside those boundaries, the value defaults to 500.
-
A negative value is not accepted.
-
If lastModifiedStartDate is not defined, then we utilize the LastRunTime (either as a parameter override, a data feed token, or the default value in the JS code).
-
LastRunTime always incorporates the lastRunTimeOffset parameter when determining a date. (Required)
-
-
If lastModifiedStartDate is set in future from current date, then we utilize the LastRunTime (either as a parameter override, a data feed token, or the default value in the JS code).
-
LastRunTime always incorporates the lastRunTimeOffset parameter when determining a date. (Required)
-
-
ISO-8601 date/time format
-
Date/Time
-
Example: 2024-10-28T01:00:11
-
We assume UTC and add the 'Z'
-
-
-
UTC format
-
Example: 2025-02-27T17:04:18Z
-
-
UTC offset format
-
Example: 2012-12-28T18:12:33+01:00
-
Example: 2021-08-04T13:00:00-03:00
-
-
-
If lastModifiedEndDate is not defined, then default to Current Date.
-
If lastModifiedEndDate is set in future to current date, then default to Current Date
-
ISO-8601 date/time format
-
Date/Time
-
Example: 2024-10-28T01:00:11
-
We assume UTC and add the 'Z'
-
-
-
-
UTC format
-
Example: 2025-02-27T17:04:18Z
-
-
UTC offset format
-
Example: 2012-12-28T18:12:33+01:00
-
Example: 2021-08-04T13:00:00-03:00
-
-
A value of the lastModifiedStartDate data feed parameter override
-
Example: lastModifiedStartDate= 2025-01-01T10:04:01Z
-
Example: lastModifiedStartDate= <LastRunTime>
-
-
A specific date as data feed parameter override
-
Example: LastRunTime = 2025-02-27T17:04:18Z
-
-
Data feed token
-
Data Feed Manager → Run Configuration tab under Tokens section.
-
-
Default value in the JS code: 1970-01-10T00:00:00Z
-
Increase value to allow more retry requests sent to a API that has errored or faulted.
-
Decrease value to limit amount of retry requests sent to a API that has errored or faulted.
-
10000 (10 seconds)
-
60000 (1 Minute)
| Key | Default Value | Possible Values (if applicable) | Description | Type (Index, Date, or Both) |
|---|---|---|---|---|
|
nvdUrl
|
https://services.nvd.nist.gov/rest/json/cves/2.0 |
|
CVE API used to easily retrieve information on a single CVE or a collection of CVE from the NVD. |
Both |
|
apiKey
|
Optional Default = [empty] |
|
The presence of the API key affects the rate of API requests. https://nvd.nist.gov/developers/request-an-api-key For API requests without API Key, the limit is 1 request per minute. The NVD API at first allows 10 requests per minute and eventually restricts API requests to 1 request per minute. |
Both |
|
type |
DATE |
DATE, INDEX |
This parameter dictates what CVE records are obtained via a specified request URL to NVDs API. This parameter can be set to either DATE or INDEX. If type = DATE: If type = INDEX: If type is Undefined Note: The best, most efficient, practice for keeping up to date with the NVD is to use the date range parameters to request only the CVEs that have been modified since your last request. |
|
|
resultsPerPage |
1500 |
|
This parameter specifies the maximum number of CVE records requested to be returned in a single API response. |
Both |
|
lastModifiedStartDate
|
<LastRunTime> |
|
Parameter used to filter CVE results based on the date a vulnerability record was last modified. lastModifiedStartDate and lastModifiedEndDate are parameters used together to return only the CVEs that were last modified during the specified period. Input formats must be in the following: |
DATE |
|
lastModifiedEndDate |
Null |
|
Parameter used to filter CVE results based on the date a vulnerability record was last modified. lastModifiedStartDate and lastModifiedEndDate are parameters used together to return only the CVEs that were last modified during the specified period. Input formats must be in the following: |
DATE |
|
requestsPerMin |
2 |
|
Puts a limit on how many API requests are made per minute to NVD’s API. Note: NVD has invoked a public rate limit (without an API key) of 5 requests in a rolling 30 second window; the rate limit with an API key is 50 requests in a rolling 30 second window. Requesting an API key significantly raises the number of requests that can be made in a given time frame. However, it is still recommended that your application sleeps for several seconds between requests so that legitimate requests are not denied, and all requests are responded to in sequence. |
BOTH |
|
lastRunTime |
Null |
|
A parameter that is used to define the lastModifiedStartDate which is passed to the NVD API. LastRunTime can be defined by the following: LastRunTime always incorporates the lastRunTimeOffset parameter when determining a date. (Required) |
DATE |
|
lastRunTimeOffset |
-2 |
|
Utilized against the LastRunTime. Adds the negative number of days off LastRunTime. Typically leveraged to ensure there is adequate overlap accounting for time offsets when extracting data. |
DATE |
|
noRejected |
true |
true, false |
By default, the NVD API includes CVE records with REJECT or REJECTED status. This parameter excludes out CVE records with REJECT or REJECTED status from being collected via NVDs API response. A value of true indicates do not return of CVEs with a Rejected status. |
BOTH |
|
proxy |
Null |
|
Provides the address of the proxy server. This is required for data feeds in SaaS. |
BOTH |
|
verifycerts |
false |
true, false |
A default verify check for user authorization - an extra layer of debugging and testing when set true. |
BOTH |
|
maxRetry |
5 |
Various |
When an exception occurs, this value indicates the number of times the script should retry the request made to NVDs API before allowing the feed to fault. If this key is not defined, any exception that is encountered will cause the feed to fault. |
BOTH |
|
retryDelay |
5000 milliseconds (5 seconds) |
Various (milliseconds time-based) Example values: |
Time period before retrying API request to NVDs API when an error occurs. |
BOTH |
|
timeout |
60000 (milliseconds) |
|
Time period between a request sent and data response from NVDs API. |
BOTH |
Important: The keys and values are case-sensitive and cannot include extra spaces at the end of the strings. The listed values are in place by default but can be configured to suit your environment.
Populate initial data
To complete a base load of the NVD data feed, set the following parameters:
-
type= INDEX
-
resultsPerPage = 1000 (client discretion, less than 2000)
-
requestsPerMin = 10 (client discretion, less than 60)
After completing the initial data load, complete the following:
-
Change the type parameter to 'DATE'.
-
Set lastModifiedStartDate to <LastRunTime>
-
Set lastRunTimeOffset to -1 (client discretion)
-
Set resultsPerPage to 1000 (client discretion, less than 2000)
-
Set requestsPerMin to 20 (client discretion, less than 60)
-
For each key type, determine whether you want it to be Protected or Plain Text. Selecting Protected encrypts the key value for the specified key in the log.
-
Click the Source Definition tab. Click the Tokens sub-tab. Verify token values.
-
The following table describes token values to verify.
Token
Value
LastRunTime
(Populated by feed)
Note: For more information about tokens, see "Data Feed Tokens" in the Archer Online Documentation.
-
Verify that key field values are not missing from the data feed setup window.
-
Click Save
The following are the mappings of the source and target fields in the data feed.
|
Source Field |
Target Field |
|---|---|
|
ID |
ID Title |
|
CVSS_V2_Access_Complexity |
NVD CVSS V2 Access Complexity |
|
CVSS_V2_Access_Vector |
NVD CVSS V2 Access Vector |
|
CVSS_V2_Authentication |
NVD CVSS V2 Authentication |
|
CVSS_V2_Availability_Impact |
NVD CVSS V2 Availability Impact |
|
CVSS_V2_Base_Score |
NVD CVSS V2 Base Score |
|
CVSS_V2_Confidentiality_Impact |
NVD CVSS V2 Confidentiality Impact |
|
CVSS_V2_Exploitability_Score |
NVD CVSS V2 Exploitability Score |
|
CVSS_V2_Impact_Score |
NVD CVSS V2 Impact Score |
|
CVSS_V2_Integrity_Impact |
NVD CVSS V2 Integrity Impact |
|
CVSS_V2_Severity |
NVD CVSS V2 Severity |
|
CVSS_V3_Attack_Complexity |
NVD CVSS V3 Attack Complexity |
|
CVSS_V3_Attack_Vector |
NVD CVSS V3 Attack Vector |
|
CVSS_V3_Availability_Impact |
NVD CVSS V3 Availability Impact |
|
CVSS_V3_Base_Score |
NVD CVSS V3 Base Score |
|
CVSS_V3_Base_Severity |
NVD CVSS V3 Base Severity |
|
CVSS_V3_Confidentiality_Impact |
NVD CVSS V3 Confidentiality Impact |
|
CVSS_V3_Exploitability_Score |
NVD CVSS V3 Exploitability Score |
|
CVSS_V3_Impact_Score |
NVD CVSS V3 Impact Score |
|
CVSS_V3_Integrity_Impact |
NVD CVSS V3 Integrity Impact |
|
CVSS_V3_Privileges_Required |
NVD CVSS V3 Privileges Required |
|
CVSS_V3_Scope |
NVD CVSS V3 Scope |
|
CVSS_V3_User_Interaction |
NVD CVSS V3 User Interaction |
|
DFMKey |
DFMKey |
|
NVD_Link_Helper |
NVD Link Helper |
|
Source |
Source |
|
Summary |
Description |
|
Vuln_Last_Mod_DateTime |
NVD Last Modified Date |
|
Vuln_Pub_DateTime |
NVD Vulnerability Published Date |
|
DFM_Key(VULN_REFERENCE_LIST) |
DFMKey (Vulnerability Reference Lists) |
|
Types->ListValues->ListValue |
Type (Vulnerability Reference Lists) |
|
URL |
URL (Vulnerability Reference Lists) |
Important: A data feed must be active and valid to successfully run.
As you schedule your data feed, the Data Feed Manager validates the information. If any information is invalid, an error message is displayed. You can save the data feed and correct the errors later; but the data feed does not process until you make corrections.
-
Go to the Schedule tab of the data feed that you want to modify.
-
From the menu bar, click
 .
. -
Under Integration, click Data Feeds.
-
Select the data feed.
-
Click the Schedule tab.
-
-
Go to the Recurrences section and complete frequency, start, and stop times, and time zone.
-
Field
Description
Frequency
Specifies the interval in which the data feed runs, for example, Minutely, Hourly, Daily, Weekly, Monthly, or Reference.
-
Minutely. Runs the data feed by the interval set.
For example, if you specify 45 in the Every list, the data feed executes every 45 minutes.
-
Hourly. Runs the data feed by the interval set, for example, every hour (1), every other hour (2) and so forth.
-
Daily. Runs the data feed by the interval set, for example, every day (1), every other day (2) and, so forth.
-
Weekly. Runs the data feed based on a specified day of the week, for example, every Monday of the first week (1), every other Monday (2), and so forth.
-
Monthly. Runs the data feed based on a specified week of the month, for example, 1st, 2nd, 3rd, 4th, or Last.
-
Recurrence. Runs a specified data feed as runs before the current one. This option indicates to the Data Feed Service that this data feed starts as soon as the referenced data feed is completed successfully. For example, you can select to have a Threats data feed run immediately after your Assets data feed finishes. From the Reference Feed list, select after which existing data feed the current data feed starts.
A reference data feed will not run when immediately running a data feed. The Run Data Feed Now option only runs the current data feed.
Every
Specifies the interval of the frequency in which the data feed runs.
Start Time
Specifies the time the data feed starts running.
Start Date
Specifies the date on which the data feed schedule begins.
Time Zone
Specifies the time zone in of the server that runs the data feed.
-
-
(Optional) To override the data feed schedule and immediately run your data feed, in the Run Data Feed Now section, click Start.
-
Click Save.
Certification environment
Date Tested: September 2025
|
Product Name |
Version Information |
Operating System |
|
Archer |
2025.04 |
Virtual Appliance |